Although it may seem prudent to immediately announce a consumer-data theft in the post-Equifax era, SunTrust Banks probably made the right call to wait weeks before disclosing its own breach, security and other experts said.
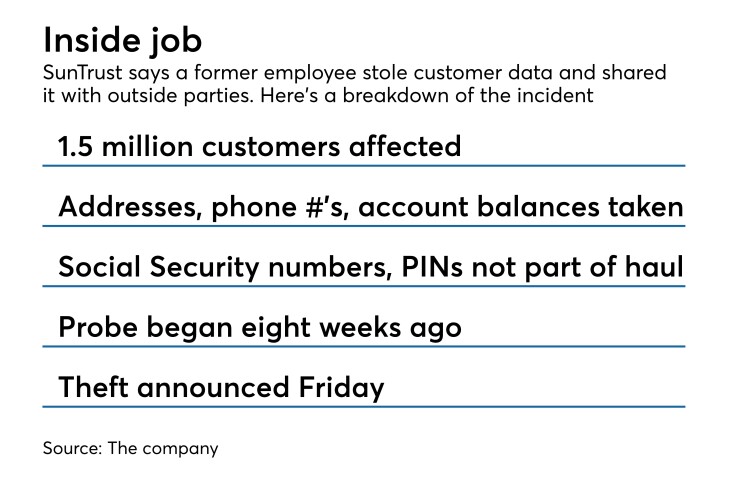
A former employee appears to have illegally accessed
SunTrust has not yet detected fraud, and more sensitive personally identifiable information like Social Security numbers were not stolen, the company said.
Although SunTrust learned of the theft in late February, CEO William Rogers said he decided to publicly disclose the incident only after the bank discovered the information may have been distributed outside the company.
“We believed until late last week that the information did not leave SunTrust,” Rogers said during a conference call with analysts Friday. “Late last week, we received new information and learned that there was a possibility of external exposure of information. Once I learned there was even a possibility of external exposure, that triggered my decision to disclose this to the clients and owners.”
SunTrust began its investigation immediately upon learning of the incident, and it hired outside experts to help gather facts, a company spokeswoman said.
It would make sense for SunTrust to hold off an announcement until it confirmed exactly what happened, said Robert Braun, a cybersecurity attorney at Jeffer Mangels Butler & Mitchell in Los Angeles.
“The real question is, what did SunTrust know and when did they know it?” said Braun, who is not involved in the company’s investigation. “You don’t know what they were discussing with law enforcement. They may not have known if there actually was a breach.”
Law enforcement agencies frequently advise companies that have been victimized to delay informing the public about a breach, said Jim Koenig, a privacy and cybersecurity attorney at Fenwick & West in New York.
Law enforcement may be “pursuing evidence against the external threat actor, or a knowledgeable insider,” said Koenig, who also is not involved in SunTrust’s investigation.
Since a former employee was involved, and not an outside hacker, SunTrust had to conduct a much more delicate investigation, said Chris Marinac, an analyst at FIG Partners.
“These incidents usually require internal intelligence gathering, and therefore are unlikely to be immediately announced to the public,” Marinac said.
Nevertheless, it is important for companies, especially in the financial services sector, to inform customers in as timely a manner as possible about a data breach, said Suresh Ramamurthi, chairman of the $33 million-asset CBW Bank in Weir, Kan., and a finalist for American Banker’s
“The sooner customers know, the sooner they can protect their information and credit,” Ramamurthi said.
Equifax was criticized for waiting months between the time of its cyberattack, which
They are “trying to balance the urgency of public disclosure versus taking the time to get the count and facts correct,” Koenig said.
In many other incidents of data theft, companies have waited far longer than SunTrust did to make a public announcement. In that respect, SunTrust “was not off the reservation” in waiting several weeks, Braun said.
However, SunTrust still could have been more aggressive in probing for information and alerting the public. When a former employee has illegally accessed information, that is usually a sign something bad has happened, Braun said.
Although SunTrust said some of the most sensitive forms of personally identifiable information were not stolen, details like customer names, addresses and phone numbers still have value to hackers, Braun said.
“That information is enough to allow bad guys to do bad things,” he said.
Finally, the way SunTrust announced the breach raised eyebrows, both Marinac and Braun said. Rogers disclosed the incident during a Friday morning conference call with analysts to discuss first-quarter earnings. The company did not issue a press release about the breach until after the call.
Announcing the incident during the call was “highly unusual,” Marinac said. “The way they disclosed it is kind of an odd way to do it,” Braun said, adding that he did not know of other companies that verbally communicated the existence of a breach during a conference call.
SunTrust declined to comment about how it disclosed the incident.











