Cybercrooks may find hacking into the payment network of a small business relatively simple, but they can hit the mother lode if they find a way into a corporation’s bank account.
Commercial banks with large corporate or business clients have no room for error in establishing security measures against growing malicious software and other online attacks specifically targeting them, a data security and fraud expert indicates in a new report.
“It is much easier to be a successful bad guy than a successful good guy because a criminal who is successful in one of 100 attempts will make off with a tidy sum,” says Julie Conroy McNelley, senior analyst with Aite Group and co-author of “Banks and Businesses in the Crosshairs: Cybercrime and Its Impact.”
“Banks, on the other hand, must seek perfection in their attempts to protect themselves and their customers,” McNelley tells PaymentsSource.
An overview of the risks facing the retail and commercial banking industry and the priorities for online and mobile fraud-protection spending highlight the first of five parts of the cybercrime report Boston-based Aite Group will release through early 2012.
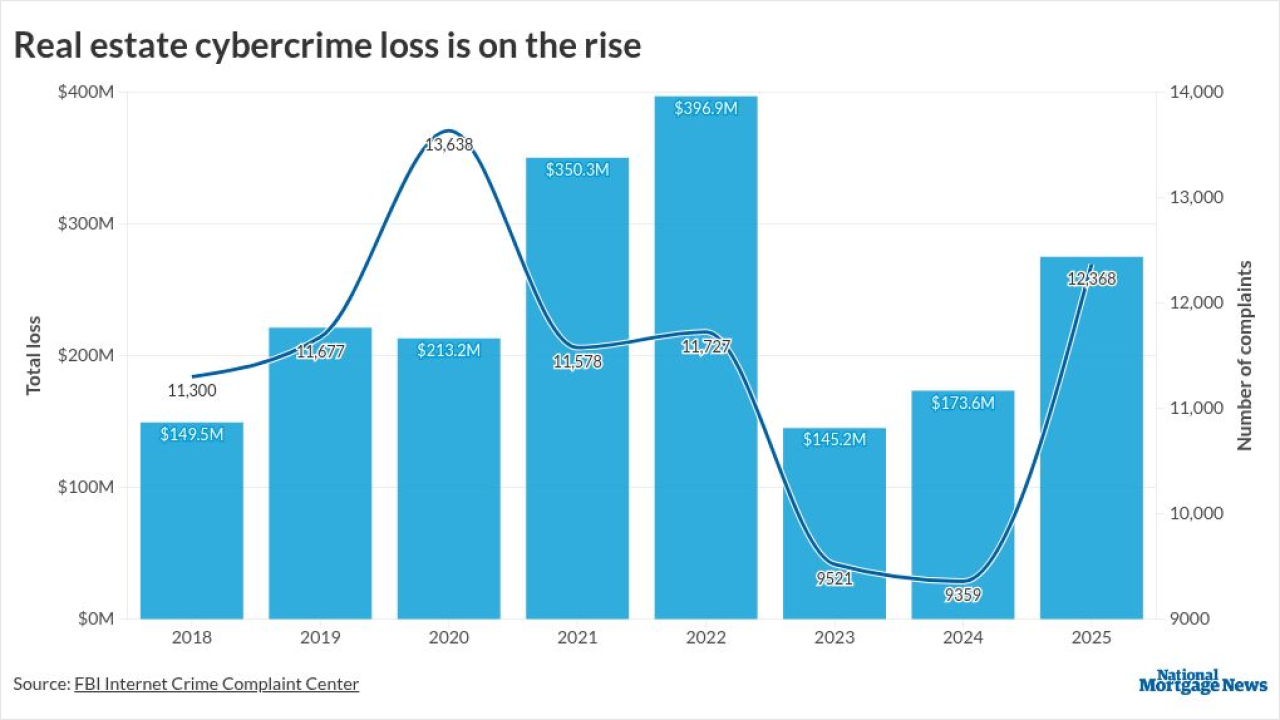
Corporate-account takeovers could result in as much as $210 million in losses this year and could reach $371 million by 2015, the report estimates.
Meantime, hackers could release as many as 25 million new strains of malware by the end of 2011, and the total could grow to 87 million by the end of 2015, the report indicates.
“The commercial online and mobile channels need the highest priority for fraud protection,” McNelley says.
Fraud at the consumer point of purchase represents “a steadily dripping faucet” by taking a little money all of the time, but commercial-account fraud represents “a big boulder that falls on you” because of the loss of dollars and the domino effect on a bank’s tarnished reputation, McNelley says.
Moreover, several victims of corporate-account takeover have sued their financial institution, alleging a lack of risk controls in place, she adds.
A corporate-account takeover often originates when an employee, such as the company controller, logs on to the company’s online banking website to transfer funds or confirm deposits after having surfed the Web or opened an email attachment that downloads key-logger malware, McNelley explains.
“The criminal will see every keystroke the controller is making on the banking website and will stay there until he is off, and then drain the account,” McNelley says.
Though cybercrime is on the rise, so, too, is the number of defenses financial institutions are deploying to fight back, the report notes.
Layered security, or deploying multiple defense mechanisms, is far more common at banks than it was just five years ago, and many of the leading financial institutions have used that approach for several years, the report reveals.
In an indication that large corporate accounts are not the only targets, the Federal Bureau of Investigation identified 20 incidents between March 2010 and April 2011 in which the online banking credentials of small to midsize businesses were compromised and used to initiate wire transfers to Chinese economic and trade companies, the report states.
The Aite report and others like it carry a similar theme, which is that cybercrime is growing and taking on many forms (
What do you think about this? Send us your feedback. Click