Like many bankers on both sides of the Atlantic, HSBC’s Dan Johnson sees great benefit in digital identity systems for financial institutions and their customers. But he also sees a big obstacle.
In a word: liability.
“When things go wrong — not if, when things go wrong — who’s culpable?” Johnson, the head of digital identity at HSBC, said Monday, during a presentation at the Cloud Identity Summit in Chicago. “How is it going to work? What happens when bad actors get introduced into the system?”
Banks such as
Conversely,
“All of that maintenance, all of that effort costs the bank a lot of money to do, but also it’s a horrible user experience,” said Johnson, who is based in London and joined HSBC in October 2014.
In so-called
Of course, using Facebook to connect to Candy Crush is decidedly lower stakes than using your Chase credentials to open a Wells Fargo account.
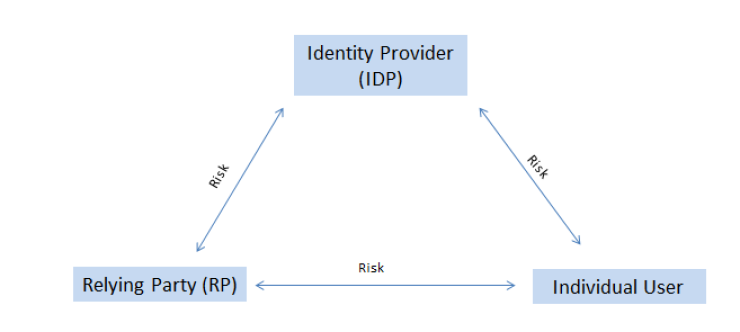
“We’ve got high risk between all three parties,” said Jeremy Grant, managing director for technology business strategy at the law firm Venable, in a separate presentation at the conference. “Without any certainty as to how the risk would be mitigated or allocated in a federation system, the market is stalled.”
Virginia is trying to solve the impasse. In 2015, Gov. Terry McAuliffe signed a law that creates a legal framework for identity systems and limits liability for identity providers if they follow high standards and best practices.
In theory, this should reduce the risk to the system, but if the standards aren’t strong enough it could just transfer risk from the providers to individuals and relying parties, further discouraging participation, Grant cautioned. He sits on an advisory
But banks would need a lot to change before they would partake in this sort of outsourcing of identity provision. At the moment, they are clearly liable, under anti-money-laundering and know-your-customer rules, if they provide accounts to bad actors, wittingly or not. (HSBC knows this all too well. In 2012, two years before Johnson came on board, the international bank paid a
“We need regulatory change so we can accept data without necessarily having to check that data,” Johnson said. “That new model needs to be created in order to allow for digital identity to work successfully in the financial sector.”
More broadly, governments would need to endorse identity systems for the public to trust them, and they’d have to work together to make identities globally interoperable.
“You should be able to take an identity created in the U.S., for example, and then open a bank account in the U.K.,” Johnson said. “You shouldn’t need to have to prove residency. You shouldn’t need to turn up in a branch in the U.K. ... You should be able to assert your identity, your U.S. identity, in the U.K. — providing that the U.K. government trusts the U.S. government and vice versa.”
While Johnson played it close to the vest about HSBC’s plans during his presentation, he hinted that the bank envisions itself as a potential
“There are lots of identity providers. There aren’t so many identity consumers,” he said, noting that in most existing schemes in which the private sector provides identity, the government tends to be the sole relying party.
To make digital identity portable, “we need a set of rules and a set of standards that allow us to be able to consume that data and fundamentally not have to check that data against other sources,” Johnson said. “Otherwise we’ve just added to our already existing workload.”










