Banks are focused on protecting their own mobile services against hacking attempts. But they also need to consider guarding against the possibility of an entire mobile network being compromised.
The credit bureau Experian predicts that a major wireless carrier will be hacked in 2019. While the likelihood of this doomsday scenario is debated among cybersecurity experts, a breach on so many consumers' phones could compromise a massive amount of personal information. The prediction especially raises concerns about U.S. banks' delivery of one-time passwords through SMS messages, which can be easily intercepted by hackers.
Consumers leave personal information like copies of passports in plain text on apps that are not encrypted, said Michael Bruemmer, vice president of Experian data breach resolution.
“In this case, the hackers could execute a 'jackpot' to the customer’s direct deposit account,” Bruemmer said, using a term for cyberattacks that trick automated teller machines into spewing out money from victims' accounts.
The credit bureau’s prediction is based on its monitoring of breaches, he explained; since 2003, Experian has serviced about 25,000 data breaches, with 5,100 occurring in 2017.
Radius Bank in Boston pushes out quarterly messaging to its customers about updating their mobile phones, and it regularly assesses the vulnerability of its mobile app vendor, Narmi, said Joe Mancini, vice president of security at the $1.2 billion-asset bank.
“The average consumer, if they properly enable security on their devices, is minimally exposed in this case,” Mancini said. Radius encourages customers to regularly update their phone software, avoid logging into apps on public Wi-Fi, and use multifactor authentication for opening lock screens.
To back its prediction, Experian noted a Canadian news broadcaster’s investigation into the vulnerability of Signaling System No. 7 (SS7), a telecom protocol for exchanging digital information. The protocol facilitates phone, data and billing connections, and the investigation was able to track a mobile phone and access its contents with only the phone number.
The Telecommunications Industry Association could not be reached for comment about the possible SS7 vulnerability, but some security experts say the concern is exaggerated.
Experts note breaching the SS7 protocol would require knowledge of the protocol, devices within the vicinity of the target and technical expertise to pull off the attack.
“You’d have to attack people on an individual subscriber basis,” said Al Pascual, head of fraud and security at Javelin Strategy & Research. “If you had the time and energy and wherewithal it could be done, but it could not be done easily, even for a nation state.”
Still, an overlooked security threat can become a huge liability for a corporation — just consider the fallout from the
One stopgap against a mass hacking attack is the encryption of mobile banking app communications, said Paul Benda, senior vice president of risk and cybersecurity policy at the American Bankers Association.
“Even on any public Wi-Fi, if you’re using a mobile app from a bank with encrypted communications, once you’re in that secure envelope, that information is protected,” Benda said.
But Benda acknowledged that protective measure does not help customers who keep login and password credentials on their phone in a notes application, for example. Also, the ABA recommends that customers avoid connecting to public Wi-Fi.
If a massive mobile carrier attack were to happen, banks could thwart hacking attempts performed by the malware by installing application-shielding technology, said Frederik Mennes, senior manager of market and security strategy at the Chicago cybersecurity firm OneSpan.
Banks should already be using this technology because of the frequency of overlay attacks, wherein hackers lay a window over the banking app itself, tricking consumers into handing over their login credentials, he said.
Mennes estimates that currently 5% to 10% of U.S. financial institutions use application-shielding technology, which is typically deployed before the application is released in the app store.
Artificial intelligence could provide banks another defensive measure, said Will LaSala, director of security solutions and a security evangelist for OneSpan. With most banks investing in artificial intelligence and machine learning solutions that monitor systems, they could change the login requirements for their customers in such an event.
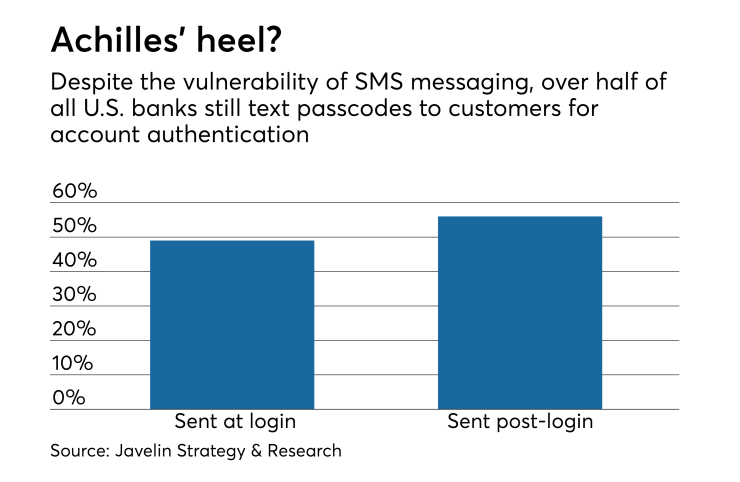
Experian’s warning about vulnerabilities in the SS7 protocol brings up again the need for banks to stop texting one-time passwords to customers for account authentication, as they can be easily intercepted by hackers, Mennes said.
According to Javelin’s Pascual, 49% of the top financial institutions in the U.S. use one-time passcodes through SMS as a login factor and 56% use it as part of step-up authentication, which is authentication used for post-login situations where an organization has identified a risk factor that warrants additional security.
Mennes recommends that banks embed two-factor authentication into the app. The mobile app would in this case contain a cryptographic key and use that to calculate a one-time password that the app would send to the bank server.
Banks could also send push notifications through the device rather than through SMS, Pascual said.
While hackers have stepped up attacks on mobile apps, customer error remains the favored way to steal personal information.
“Generally attackers are trying to perform phishing attacks to get credentials so that they can later be sold and used by other attackers to gain access to money inside the accounts, or ways to launder money in an undetected way,” LaSala said.
“As such, consumers worry about attackers gaining access to other parts of data on their device, but generally those attackers only want the data inside the financial application or the credentials to gain access to the financial account.”