-
Authentication methods meant to keep cybercriminals from taking over accounts can also lock out legitimate users. This old dilemma is growing more vexing as cybercriminals get better at impersonating customers and as regulators increasingly push multifactor authentication.
January 7 -
Moven will soon prompt its customers for usernames and passwords only for riskier transactions. By removing the login for most functions, the company aims to drive engagement in an app meant to be used on the go.
December 17 -
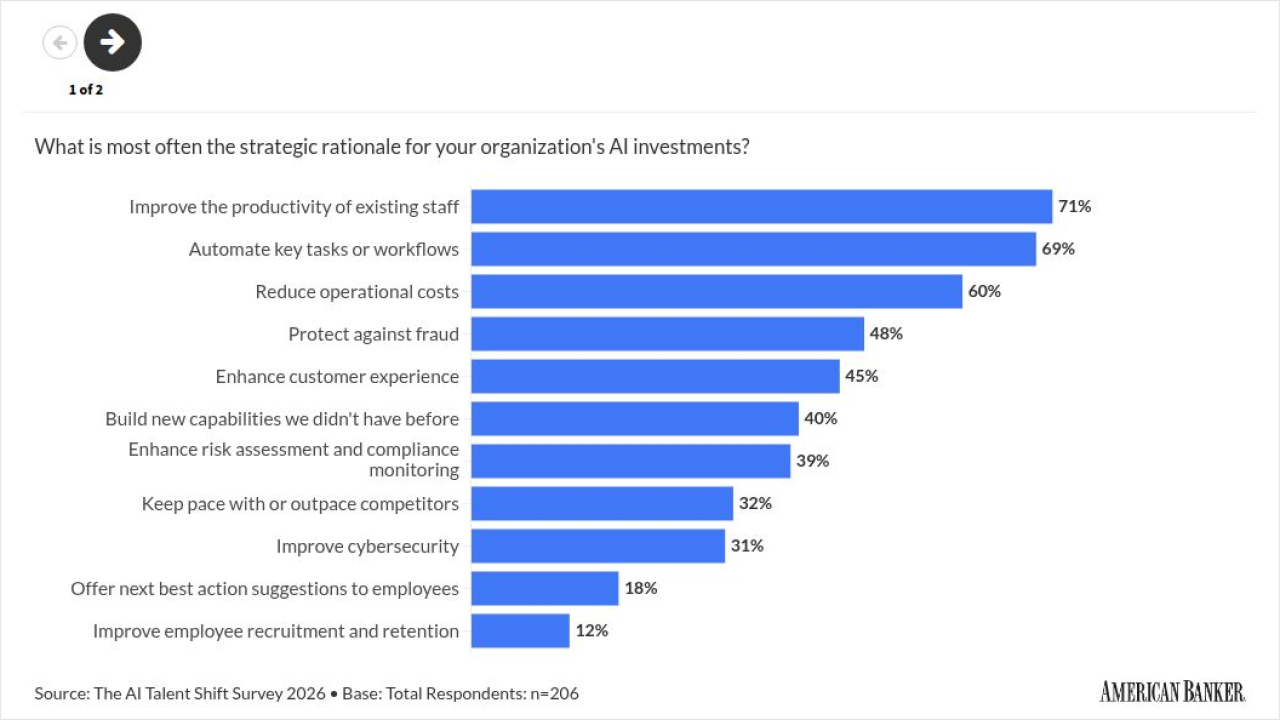
Some 75% of chief information officers plan to increase spending on security technology next year, with many anticipating jumps in security budgets of 20% or more.
October 15


Consumers have gotten used to using mobile banking, but that doesn't mean they trust it. Nor should they, given the escalating security threats.
In a recent survey, MyBankTracker, a personal finance and bank ranking platform, found that only 6% of respondents trust mobile technologies for financial transactions. When you think of how many people in this country use mobile banking — a Verizon study found that in 2015, 55% of American smartphone owners made a mobile bank transaction — this 6% is astonishing.
Another consumer study, commissioned by the security software company Arxan, found that although the vast majority of consumers — 86% — think their banks are doing enough to protect their apps, 41% expect those apps will be hacked.
"Consumers and businesses feel it's the bank's responsibility to keep them safe," said Ross Hogan, global head of fraud prevention at the security vendor Kaspersky Lab. "Many of them feel the bank is actively doing something, but just don't feel ultimately secure. They're responding out of emotion — 'I don't have any information or evidence as to what my bank is doing, but I would hope they are doing something.' At the same time, they feel vulnerable because they don't understand what steps the banks are actually taking."
Consumers don't seem to have specific fears, such as that their devices will be stolen or that mobile malware will steal their mobile banking credentials. They have a general sense that nothing passing over the Internet is safe, fed by news stories about governments and retailers like Target suffering data breaches.
"It's a perception thing," said Alex Matjanec, CEO and co-founder of MyBankTracker. "They look at Target, Netflix, Time Warner Cable, they assume there's nothing they can do."
Banks can't afford to be so fatalistic. The have to be hyperaware of the threats to mobile banking, and keep them at bay.
For years now, the common wisdom has been that banking on a smartphone is safer than using a laptop or desktop. Device identity technology that many banks use can check whether the smartphone in use is the one originally registered with the account. Geographic location data can be monitored to see whether the consumer's phone is in a logical place relative to her recent transactions, and patterns of behavior on the device can be monitored and compared against the current user's taps.
Yet, a growing body of evidence is undermining this argument, and vulnerabilities are turning up even in Apple's famous "walled garden."
Mobile Malware
Cybercriminals are stepping up their production of malicious apps that target phones and tablets — especially malware strains aimed at mobile access to bank accounts. Kaspersky Lab researchers found 39% more strains of mobile banking Trojans were developed in 2015 than in 2014, for a total of 25,000 (the number of mobile malware programs overall rose 188% during the same time period).
Most of these are Android apps, but not all.
"When you hear of mobile banking
Faketoken.AndroidOS is a mobile app used to redirect mobile transaction authentication numbers to a second device without the victim's knowledge. It was one of the leading actors in mobile malware in 2015, according to Vicente Diaz, principal security researcher at Kaspersky Lab, and it's the most prevalent threat to mobile banking today, according to the company. Faketoken ranks seventh on Kaspersky's list of the top 10 banking malware families.
"This is the first time we've seen mobile malware crack the top 10," Diaz said. There's also a second mobile malware family on the list, called Marcher, at No. 8.
Many of the new strains are ransomware, which locks the user's device and presents a demand for money to unlock it. Consumers are more likely to fall victim to ransomware on their mobile phones than on their desktop computers, Hogan said.
"If we're online and we see something that seems suspicious, we're all trained to try and circumvent it in any way possible," he said.
Many people, tethered to their phones at almost all times, may cave in to the demand for money out of frustration. "They don't care if it might be suspicious, they just want to get it over with so they can keep doing whatever they're doing," Hogan said.
Other types of malware include Trojans and rogue apps, which I'll address in more detail in my next post.
App Weaknesses
Another threat to mobile banking is that fact that banks' legitimate apps are not as locked down as you might think. Some bank app developers have simply Googled other banks' code and put the results in their mobile banking application, Hogan said. "It's happening more than anyone would care to admit."
Arxan recently tested 55 mobile finance apps for security vulnerabilities. Thirty-three of these apps are run by banks. Almost all contained two types of vulnerabilities.
One is lack of binary protection — the absence of a means of protecting code from being reverse-engineered. It appeared in 98% of the apps.
"If you don't have protected binary then it's quite simple to use tools that are typically free or less than $1,000 to reverse-engineer the application and convert that binary into something that's a close proxy of the source code," said Patrick Kehoe, chief marketing officer at Arxan.
Hackers can scrape out the security controls and repackage and post a virtually identical app on the app store. Apple or Google cannot recognize the difference. As users use the corrupted app, the cybercriminals could figure out the cryptographic protocols and keys used in communications between the mobile app and the back-end server.
"With the understanding of that challenge/response logic and the cryptographic keys that are being used, they can replicate that in another application and give access to the core application and run transactions they wouldn't otherwise be authorized to run," Kehoe said.
If a bank app was altered and reposted this way, savvy users who looked a little more closely could see that there are no or few reviews, and they might realize it's not legit. But less sophisticated or multitasking users could unthinkingly download the gamed app.
FireEye, a security company, recently revealed a slew of Android Trojan apps called SlemBunk that mimic the legitimate apps of 33 financial institutions in North America, Europe and Asia Pacific.
Once installed, these apps can gather authentication credentials from the fake banking apps.
FireEye researchers believe SlemBunk is being "sideloaded" from malicious websites, in some cases from porn sites. This again is an example of the danger of rogue apps and app stores, which I'll delve into further on Thursday.
The other common vulnerability in mobile banking apps that Arxan found is "transport layer vulnerability." This is a lack of properly encrypted connections as information is transported from the mobile device to the server. For instance, the
This type of attack would require a sophisticated hacker who knows the communications protocols and is able to monitor this traffic.
Kehoe suggests the financial services industry should have standards for mobile apps.
"Today there's very limited visibility around what type of security measures and practices are leveraged in the application," he said. "Ultimately, that's because most people don't want to disclose the types of security they're baking into their apps, because they feel that gives a leg up on the hacker. But I think there's a happy medium." There could be a set of approved certifiers that look at basic risks and vulnerabilities before giving a stamp of approval, for instance.
Consumer Education
Along with basic security issues, the misalignment between what people think their banks are doing and how secure they feel about mobile banking is a communication issue, Hogan noted.
"This is something banks can remedy if they take some time to improve the communication strategy to their customers, both retail and business banking customers," he said. "I have several banking relationships, all of which have mobile banking offerings. None of them communicate any of their mobile banking application security to me whatsoever. I've never gotten an email about what steps they've taken and I've never gotten a message in-app."
Messaging could be embedded in the application to explain some of the security methods banks use.
"Upon launch of the application, you could say, 'This app is secured by security vendor x,' as a reinforcement and communication to the user that there's some underlying security at play," Hogan said. And whenever a sensitive function is being called, such as the adding of a new payee or a person-to-person transaction, the bank could quickly run a malware scan.
The issues here are vast and will only grow. Banks that haven't set aside a portion of their budget to mobile app security need to make that a priority.
Editor at Large Penny Crosman welcomes feedback at penny.crosman@sourcemedia.com.