
The often-overlooked call center is getting more attention, as banks realize that stronger security on online and mobile channels has driven cybercriminals to focus their energies on conning phone reps.
They're tricking these eager-to-please call center agents into coughing up customer information or letting them reset passwords on other people's accounts.
"Fraudsters will always use the weakest plank in the door," said Gary McAlum, chief security officer at USAA. "If you're using strong authentication security but someone can call into a call center and social-engineer through the call center representative to reset their account, then that's the weak point in the network. It has to be an end-to-end holistic approach."
-
Security veterans Frank Abagnale and Ori Eisen have teamed up on a heavy-duty authentication service with no pretensions of being easy to use. Their venture, Trusona, just raised $8 million.
February 22 -
Authentication methods meant to keep cybercriminals from taking over accounts can also lock out legitimate users. This old dilemma is growing more vexing as cybercriminals get better at impersonating customers and as regulators increasingly push multifactor authentication.
January 7 -
Bank regulators will stiffen their requirements and identity theft will escalate, but banks will toughen up their defenses.
January 5
This problem made news when Apple Pay came out in September 2014. There was an immediate rash of call center fraud, as cybercriminals realized they could set up accounts using stolen credit card data. The problem has steadily grown since then.
Last year, one in every 2,900 calls coming into large banks' call centers was fraudulent, according to Pindrop Security. This year, the number is closer to one in every 2,000 calls. Among regional banks, it's more like one in 700. Pindrop's software analyzes incoming calls for signs of fraud and scores them for risk. For instance, if a call is coming from Nigeria and the same caller number has called the contact center for different accounts, it will probably end up with a high risk score. (Pindrop was one of American Banker's
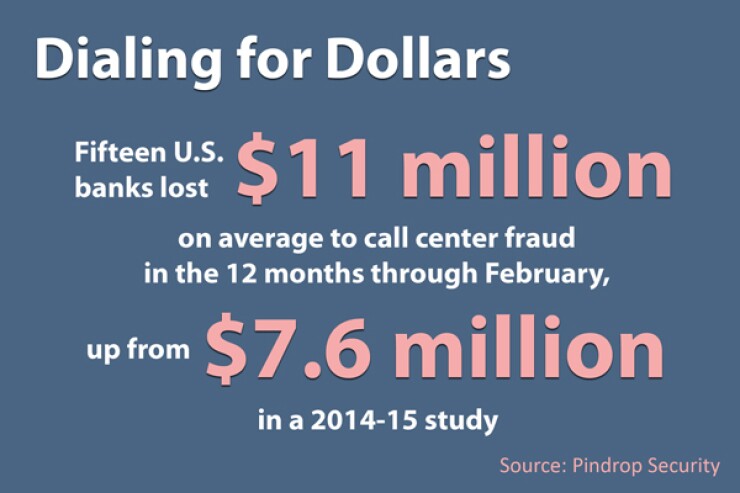
The average fraud exposure caused by these hackers — that is, the average amount they could potentially steal after successfully logging in by gaming the call center — was $7.6 million per bank in a 2014-15 study. More recently, in a study that covered the 12 months through February, it was $11 million per bank, according to Pindrop.
So the attackers have been able to expand the pools of money that they can reach by over 45%.
"When we're working with customers, we're finding about 30% to 80% of all fraud has a phone component," said Vijay Balasubramaniyan, Pindrop's CEO and chief technology officer.
Bankers are generally tight-lipped about sharing what technology they're using to better secure their call centers.
"The more information you provide to the fraudsters, the better [equipped] they are to perpetrate their fraud," said Brett Beranek, director of product strategy for voice biometrics at Nuance Communications. His company's technology analyzes incoming calls for fraud, detecting mismatches between the caller and previous recordings tied to the same account. It can also spot people calling about multiple accounts and fraudsters whose voices are on a blacklist. "The more information is disseminated, the less effective fraud groups can be at stopping the fraudsters."
Canada's Tangerine Bank recently invested in secure chat software to allow call center agents to have encrypted, archived chat sessions with authenticated customers, according to the bank's chief information officer, Charaka Kithulegoda.
Patience and PII
One reason call centers are facing a rise in fraud attempts is the prevalence of personally identifiable information, McAlum observed.
Fraudsters painstakingly gather information about account holders on the Web and use it to manipulate customer service agents who are trained to be helpful, not to block crime. The fraudster might say, "I don't remember my own password, let me call you right back." Then he'll go out to social media sites and figure it out.
"One call center agent completely buckled and started reading out every single account transaction on [a customer's] account for the last month," Balasubramaniyan said. "Though [the fraudster] didn't manage to get a wire at that point, now that he had all his transactions, he called back in, and when the next call center agent said, 'How do I trust you?' he started rattling off these transactions. The call center agent said, 'OK, it must be you,' and let him through."
Balasubramaniyan's all-time favorite call was from a fraudster who, when asked, "What's your mother's maiden name?" replied, "My dad married thrice, so can I take three guesses?"
"It doesn't even make sense — so what, your dad married thrice?" Balasubramaniyan said.
The call center agent allowed him to take three guesses, the last of which was "Smith," which is one of the most popular names in the world and happened to be right. After that call, he wired $97,000 out of the bank.
Beranek said by closely monitoring what goes on in the call centers, banks can learn how fraudsters operate.
"Often a fraudster will call in several times and progressively increase the complexity of their calls," he said. "So for call No. 1, they would ask for a benign piece of information that would be very easy to socially engineer the contact center agent to provide. By call five or seven, they have amassed enough information that they could completely take over the account, go online and perform a wire transfer."
Fraudsters often need several attempts to break into accounts, because as they search the Web for information on account holders, sometimes the data they get is correct, sometimes it isn't.
IVR Reconnaissance
In addition to live agents being fooled by fraudsters, there's an uptick in the gaming of automated interactive voice response systems, or IVRs. Cybercriminals can robo-call IVRs continuously to guess a PIN number. (If it's four digits, there are 10,000 possible combinations.)
In 2014, only 47% of calls to banks went through IVR systems. This year, more than 60% of calls will, according to Pindrop, as banks are cutting back on live agent calls. (It behooves Pindrop to point all this out, as it's getting ready to release an IVR security system that will act similarly to its call center software.)
There isn't always fraud happening within the IVR itself, Balasubramaniyan said. "What the IVR is great in is reconnaissance, which is finding out about an account without talking to a call center agent," he said. It's also good for trying different combinations of account numbers, PINs and card verification values (those three-digit codes on the backs of payment cards) without coming up on any radar.
"If you're able to detect that activity, you can forewarn banks on average 30 days before account takeover even starts happening," Balasubramaniyan said. "It's almost like 'Minority Report,' " the science fiction movie about a clairvoyant police force.
In addition to security software, of course, part of the answer is to make call center agents more aware of social engineering and help them look for signs of foul play. One of our cybersecurity
The hard part is taking a tougher stance on such helpful call center duties, without turning away legitimate customers.
Editor at Large Penny Crosman welcomes feedback at