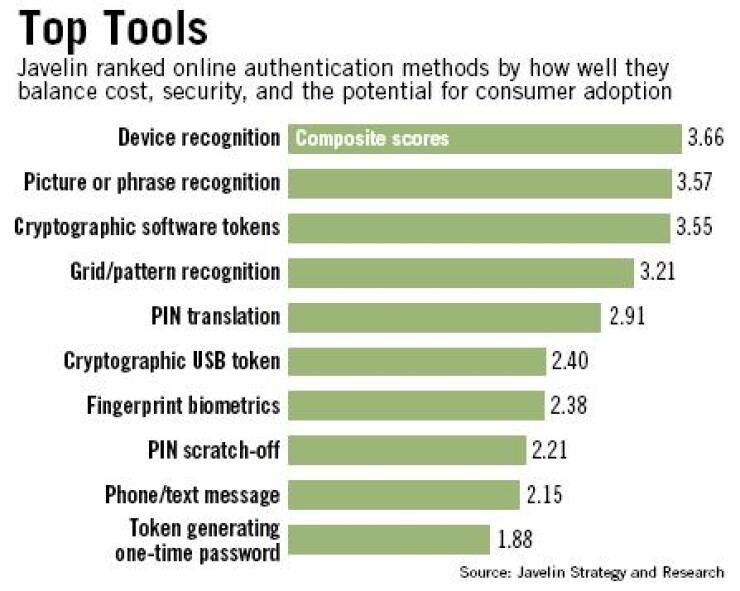
Three online authentication tools stand out from the pack for balancing a high level of security, a favorable return on investment, and a low likelihood of annoying customers, a report released Wednesday says.
The report gave the highest marks to device recognition tools, which assign an identification number to a user's computer and trigger additional authentication steps, such as a phone call or a personal question, if the user logs on from a different machine; software that asks a user to confirm a previously chosen picture or phrase when logging on to a bank's site; and downloadable password-generating software.
Banking companies will soon have to make authentication investment decisions with often-conflicting considerations in mind. Under the Federal Financial Institutions Examination Council guidelines released last month, by the end of next year banks must assess the risk to their online systems and make a good-faith effort to strengthen authentication measures for transactions deemed high-risk.
"Banks are scrambling now, and we do think it is scrambling," said Bruce Cundiff, an analyst at Javelin Strategy and Research of Pleasanton, Calif. and the report's author.
So far device recognition tools, which are largely invisible to the consumer, seem to be gaining the highest level of acceptance among bankers, Mr. Cundiff said. "It makes sense for the user, it makes sense for the institution, it's relatively easy to implement, and it's cost-effective."
Naftali Bennett, the chief executive of Cyota Inc., which sells device recognition tools, said it makes sense for bankers to install such devices.
"Before purchasing new hardware, leverage existing infrastructure," he said. "Your customers today have computers. A computer is a piece of hardware. That hardware can be authenticated."
However, Mr. Cundiff said that bankers may see one aspect of the tool often called beneficial - its invisibility to the consumer unless a transaction is deemed high-risk - as a detriment. Some banks will seek to increase market share by touting increased protection, and they will want authentication tools the consumer can see, such as picture recognition software, he said.
For example, by early next year Bank of America Corp. will require all its customers to use a picture recognition system when logging on to its site. Customers choose a picture when they first visit and are presented their choices in subsequent visits to assure them the site is not fake. Customers in California will begin using the technology this month.
Passmark Securities Inc. of Redwood City, Calif., is providing B of A with the system and the behind-the-scenes technology necessary to authenticate the customer.
"It is very customer-friendly and doesn't require the users to carry around any extraneous tokens," said Mark Goines, Passmark's chief marketing officer. It plans to announce this month that another large banking company is implementing its technology.
Mr. Cundiff said bankers should take note of B of A's approach. "It's not anything the banks can ignore. … It provides a feeling of security among consumers."
The U.S. online banking division of ING Group NV is another early adopter of a highly visible authentication tool. The division, which uses the ING Direct brand, recently added a PIN pad to its site; customers must enter their passwords on the pad using a mouse rather than a keyboard. The tool is meant to protect customers from keystroke-logging programs, which fraudsters plant on computers to monitor the user's keystrokes.
The U.K. banking company Lloyds TSB has gone a step farther. Last month it said it is giving about 30,000 customers tokens that generate a new six-digit passcode every 30 seconds. The same technology runs on Lloyds computers, so at any moment the passcode from the token should match the one at the company.
There is a downside to trying to use visible authentication tools to increase market share, Mr. Cundiff said; banks will have to spend heavily not only on the technology, but also on integrating the various departments that could be affected and promoting consumer awareness.
"How much money you are spending on the awareness campaign is the major factor," he said. "I can implement the solution, but if I don't tell anyone about it, I'm not using it to expand my cardholder base."
The third authentication tool Javelin commended for balancing cost, effectiveness, and consumer-friendliness is cryptographic software that generates a regularly changing password. Unlike password-generating tokens, this tool is downloaded directly to the user's computer. It is relatively new to the market and has not yet had any public takers, Mr. Cundiff said.
Another strategy is to implement fraud detection systems across the retail bank, not just at the Web site. For example, Fair Isaac Corp.'s Falcon One system checks identities and detects fraud in various areas, including demand deposit accounts, new applications, and account takeovers.
"You have people out there that have been selling online banking solutions, but when you look at the technology, it isn't that extensive," said Mike Lazarus, the director of product management for Fair Isaac's fraud solution department. "They're not looking to cover other channels of retail banks."
Fair Isaac introduced Falcon One in May and added a device recognition tool for online banking in August. Though bankers want to invest in technology they can leverage across their entire operation, they want to do so in phases, and online banking is often the first phase, Mr. Lazarus said.
Though the jury is still out on which tools will be the most effective in preventing fraud and keeping customers online, security experts agree that banking companies should constantly reassess their security procedures.
"Secure against today's and tomorrow's threats," Mr. Bennett said. "You don't want to implement a solution that only addresses phishing, for example, when we have a good idea of what we're in store for over the next 18 months," such as the emerging threat of Trojan horses - programs that let fraudsters control a computer remotely.