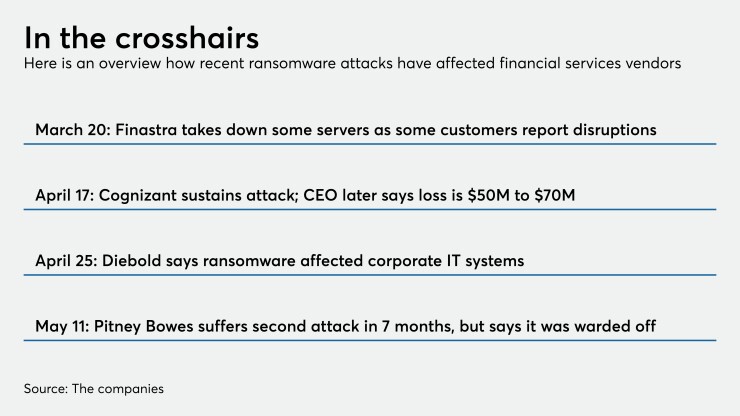
A recent rash of ransomware attacks on bank technology vendors — including Finastra, Diebold Nixdorf, Cognizant and Pitney Bowes — raises serious questions about why they're happening and what banks can do to protect themselves.
“The threat vector of ransomware is definitely concerning for the industry, not only for us as a bank but for the industry and not only for the industry but also for the regulators,” Saul Van Beurden, head of technology at Wells Fargo, said in a recent interview. To his point, regulators drew specific attention to the need to protect data in the cloud
One reason hackers are targeting these vendors now is they perceive security weaknesses in the chaos of the near-universal shift to work from home.
“The pandemic environment has created new opportunities for ransomware attacks on every bank and banking supplier,” said Gary McAlum, chief security officer at USAA.
Finastra CEO Simon Paris said
Similarly, the ransomware attack on Cognizant targeted systems the information technology services firm was using to provide laptops to employees working from home during the pandemic.
Cognizant and Pitney Bowes (which provides anti-money-laundering, branch strategy and marketing software to banks) were both hit by a ransomware gang called Maze. Earlier this year, Maze attacked Banco BCR, the state-owned Bank of Costa Rica.
Maze claims its reasons for attacking banks and tech vendors are virtuous: It's simply drawing attention to security lapses in the industry. In a press release dated April 30, the group expressed a curious set of ethics. It announced that it originally attacked Banco BCR last August, and it reprimanded the bank for not disclosing the security breach to other banks as it said state rules require.
The Maze hackers said they performed a “routine check of previously accessed systems” in February and found that no changes had been made.
“In the security perimeter was a hole the size of the Channel tunnel,” the release said. “We decided not to block the work of the bank. It was at least incorrect during the world pandemic.”
The group said it has stolen data on 11 million credit card holders that it could sell on the dark web, but that it won’t. It said its motive was to “alert people and financial institutions about the poor security.”
Like other ransomware groups, Maze runs a website where it lists victims and leaks sensitive data if they don't pay the ransom demanded. It recently began releasing payment card data from Banco BCR.
Trend started before the pandemic
In the bigger picture, the trend toward ransomware attacks was in full swing before the pandemic started.
“In January, we published our top 10 trends for cybersecurity, and our No. 1 trend was ransomware,” said Joseph Krull, senior analyst at Aite Group. “We saw that it was going to be a tsunami and it would have been a tsunami regardless of COVID-19.”
The pandemic does make cybercriminals' life easier, he acknowledged. They’ve been able to exploit people’s fears of coronavirus and need for information about what’s happening with emails offering information, help or access to government stimulus money while getting people to click on malicious links or dropping malware on their machines.
And where a worker in an office can have a colleague look at a suspicious email, working from home makes it harder to get a second opinion.
And people working from home tend to have insecure home networks.
“They may have never updated the firmware on their router,” Krull points out. “They may be using networks on which folks are doing things they shouldn't be doing, like downloading illegal games or pirated movies,” which is another good way to download malware onto a victim’s computer.
Krull also points out another significant change in the ransomware attacks on banks and their vendors. In December and January, ransomware hackers switched from merely locking up computers and demanding ransom to stealing data, posting it to a website and then locking computers.
"They're using the fact that they've exfiltrated sensitive data as an impetus to get those firms to start paying ransom,” Krull said. In some cases, the cyberthieves threaten to tell data protection authorities like the California attorney general.
Another trend is that instead of starting with a phishing attack, cybercriminals are attacking companies through poorly managed use of remote desktop protocol.
“RDP is great technology if you want to administer a network from your home,” Krull said. “But if they're using RDP without two-factor authentication, it's really easy to exploit that. It's just bad hygiene and poor behavior from systems administrators that frankly should know better.”
Bank tech vendors tend to pride themselves on their security acumen. But as Krull points out, “the hacker only has to be right once — they only have to find one vulnerability.”
Allan Liska, threat intelligence analyst at Recorded Future, a security threat intelligence firm that works with several bank tech vendors, said these companies are not as watertight as one might expect.
“They simply don't have the money to invest heavily in security the way the banks in the United States have,” Liska said.
One of the biggest security lapses among bank tech companies, he said, is insufficient knowledge of what’s on their networks.
“Having exposed servers and systems that they're not aware of is one problem,” Liska said.
Another shortcoming is having vulnerable software that hasn’t been patched properly.
A third is insufficient phishing training.
“They do an awful lot of phishing training, but it isn't enough simply because they're still getting hit by these ransomware attacks,” Liska said. “You can say that about almost any organization simply because it is really hard, especially with a large workforce, to be prepared against a phishing attack, especially as creative as the attackers have gotten.”
How banks can protect themselves
Among U.S. banks, reported ransomware attacks have declined. They were hit with 40 ransomware attacks between April 2019 and April 2020, according to Recorded Future. During the prior year (April 2018 to April 2019), they were hit 57 times. To be sure, not all attacks are reported and accurate counts are hard to come by.
“The banks have gotten much better at protecting themselves,” Liska said. “They've invested more money than almost any other sector in keeping themselves protected from ransomware attacks, which in part would explain why you're seeing so many of these attacks hit the third-party vendors that serve financial institutions. It's really, really difficult to get into the banks, but some of the vendors that serve the banks are a little bit easier to get into, and you can use that access to hopefully get into the banks.”
USAA uses an ever-changing host of methods to combat cyber risk in its supply chain, including a proactive, multilayer security model, on-site supplier visits, self-assessments and third-party monitoring services, McAlum said.
“All of these tools and data points, among others, factor into our cyberdefense program,” he said.
Phishing detection software and software patching, especially for those vulnerable RDP systems, are a must for banks that want to protect themselves from ransomware attacks. Requiring two-factor authentication for any vendor accessing their networks is another.
“If you have all of your third-party vendors using two-factor authentication, then if somebody does compromise your infrastructure, whether it's through ransomware, business email compromise or some other kind of attack, they can't just walk right into your network,” Liska said. “They would need to have that secondary code.”
Another thing banks can do is segment their networks, so that if a vendor is compromised, only the systems the vendor needs to have direct access to will be affected.