- What's at stake: Adversaries are actively intercepting financial data today so they can decrypt it later once a capable quantum computer becomes available.
- Supporting data: Google plans to complete its post-quantum cryptography transition by 2029, well ahead of the 2035 target set by NIST and the NSA's 2031 deadline.
- Forward look: Financial institutions must immediately begin inventorying their cryptographic assets and questioning vendor roadmaps to prepare for the looming "Y2Q" transition.
Overview bullets generated by AI with editorial review
Cybersecurity professionals attending cybersecurity conferences over the past four years have largely gone in expecting artificial intelligence to completely dominate the conversation.
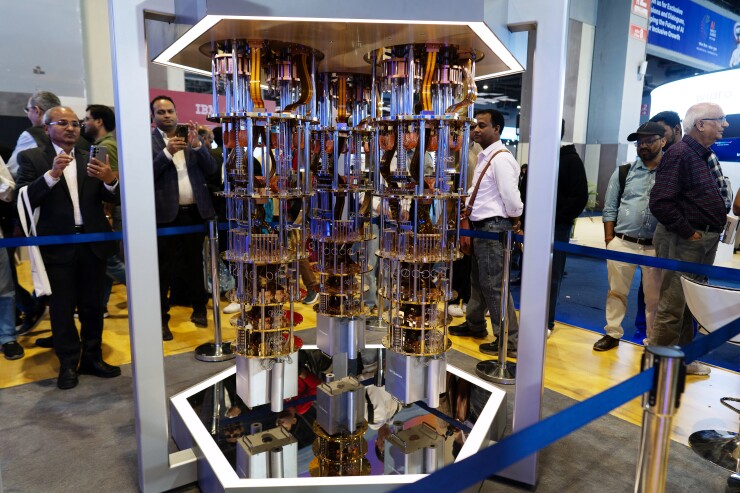
But, as 44,000 cybersecurity professionals flooded the halls of the RSAC Conference in San Francisco last week, another massive technological shift quietly commanded a huge share of the spotlight: the impending obsolescence of modern encryption.
For U.S. banks and credit unions, the transition to post-quantum cryptography represents an immediate operational imperative rather than a distant IT headache, speakers at the event said.
Adversaries are actively intercepting and hoarding encrypted financial data today, an ongoing espionage tactic the Federal Reserve recently referred to as "harvest now decrypt later." Hackers siphon up this data with the intent to crack it the moment a cryptographically relevant quantum computer becomes available.
Security experts at RSAC this year made it clear that protecting the digital trust fabric of the financial system requires banks to treat this transition as a current, present risk to the enterprise.
During a session on migration strategies, Dell Technologies security architect Mike Phillips warned that "Q-Day," the moment a quantum computer officially breaks current cryptography, will inevitably bring "exposed data, leaked credentials, and compromised systems."
As such, the financial sector is actively mobilizing to address this looming threat.
Much as companies successfully moved early to fend off the problems foretold in the late 1990s about Y2K, the cybersecurity industry is looking to avoid the problems of what some are calling Y2Q.
Perhaps the biggest difference, though: The deadline for Y2Q is not a pre-determined day. Depending on who you ask, it could arrive any time in the next 3 to 30 years.
The Financial Services Information Sharing and Analysis Center (FS-ISAC) is taking the timeline seriously. In September, the industry group urged banks to coordinate globally to immediately start the financial services industry's transition to post-quantum cryptography — starting with a timeline.
Developing a global transition timeline represents a "critical first step forward for the global financial ecosystem," according to Peter Bordow, managing director of quantum security at Wells Fargo and chair of the FS-ISAC workgroup on post-quantum cryptography (PQC).
Elevating PQC from an IT headache to a boardroom priority
At RSAC, experts stressed that financial institutions must stop viewing the post-quantum transition as a routine technology upgrade. Instead, banks need to frame the migration as a critical business risk.
During a Tuesday panel about what to do and avoid during PQC migration, Jane Yuan, a security architect at Dell Technologies, urged security teams to treat the transition as a "dependency management problem."
A single cryptographic function might rely on an open-source library, which in turn relies on another vendor that is still waiting for standards to evolve, compounding the institution's overall risk.
To tackle these sprawling supply chain issues, chief information security officers must get their executive leadership aligned. Yuan advised CISOs to speak the language of enterprise risk when talking to their corporate boards, rather than focusing on technical weeds.
"Frame your post-quantum migration actually as an enterprise risk issue and tie that migration to the existing business strategy," Yuan said.
Amit Sinha, CEO of digital security firm DigiCert, said that he has seen a change over the past three years as the company has been promoting PQC transition.
Concrete industry deadlines discussed at the conference underscore the urgency of these boardroom conversations. Sinha pointed out that Google recently announced that it plans to complete its PQC transition by 2029, far in advance of the 2035 target set by NIST and the NSA's 2031 deadline for national security systems.
Financial institutions step to the forefront of 'Y2Q'
The banking industry is leading the charge to prepare for "Y2Q," the anticipated deadline when quantum computers will boast enough processing power to break the encryption algorithms currently securing the internet, according to Deepak Behal, an information security officer for Capital One.
"Y2Q is a moment when quantum computers become powerful enough to break today's public cryptography," Behal said during a Thursday session.
While exact timelines vary, many experts believe this threshold is only five to ten years away, he said.
Geopolitical pressures are also accelerating the financial sector's push to modernize its encryption. Global adversaries are already treating quantum-safe cryptography as a national security priority.
"China has put out a press release" announcing that the country is "doubling down on PQC," according to Sinha. The Chinese government designated finance, government, and energy as the "first areas to hit" in this migration, he said.
To defend against these looming threats, conference speakers repeatedly urged banks to launch comprehensive cryptographic inventory initiatives immediately.
"You cannot secure what you cannot see," Behal said, explaining that a bank's first job is to locate every instance of vulnerable encryption, whether it lives on-premises, in the cloud or with a third party.
Knowing exactly where public key infrastructure assets currently reside is the foundational first step for any modernization effort, Sinha said.
This inventory process is an especially important part of third-party risk management, according to Dell's Yuan. She warned that the most critical risks for an organization often sit with external vendors and partners.
As such, financial institutions must begin interrogating their vendors and partners about their specific post-quantum roadmaps to avoid downstream supply chain vulnerabilities.
"When you talk to your suppliers, you should ask the same question as you ask your internal," she said, noting that banks must ask vendors directly about their quantum roadmaps and timelines.
Colliding forces: AI's role in executing the cryptographic migration
Artificial intelligence and quantum computing represent two of the largest technological shifts facing the financial sector, and experts at RSAC predicted they will inevitably collide during the cryptographic migration.
AI can accelerate the migration by assisting banks with "cryptodiscovery, flagging brittle patterns," and refactoring legacy systems to support crypto-agility, according to Dell's Phillips.
However, relying on autonomous agents to write and implement cryptographic code also carries immense risks.
AI models might generate non-compliant code, Phillips warned, noting that "whether a human generates the crypto code or whether it comes from an autonomous agent, it has to follow the same standard crypto rules" and strict post-quantum timelines.
Bank security leaders must employ a "trust but verify" mandate when evaluating any AI-generated defenses, he said.
Navigating this dual disruption requires financial institutions to fundamentally rethink how they protect their digital trust fabric, according to Michele Mosca, CEO of cybersecurity firm evolutionQ.
Mosca warned during a panel on the closing day of RSAC that the public key infrastructure the banking industry uses currently lacks a cohesive "cryptographic strategy" — a strategy for PQC transition that aligns with broader enterprise risk management frameworks.
Institutions must do the hard work of integrating "cryptographic risk management" directly into their enterprise risk frameworks, Mosca said, before adversaries can compromise today's encryption — whenever that happens.