Handy Feature
Ogaki Kyoritsu Bank in Japan will use

Heart to Heart
Heartland Payment Systems'
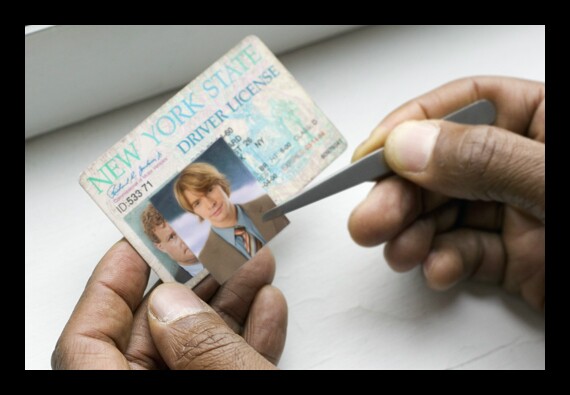
Bad Deal
An online fake ID shop was also
Mac Under Attack
Apple's computers

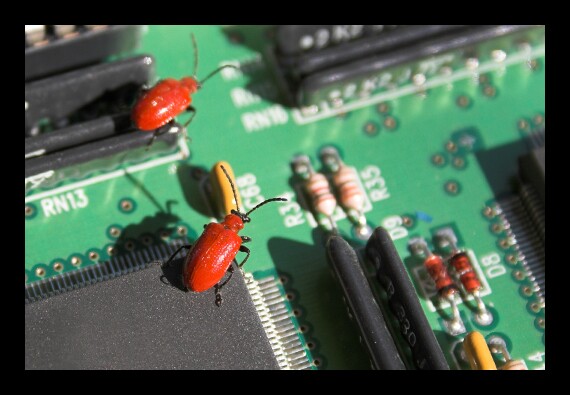
Persistence Pays
Advanced persistent threats, which have no known signature or pattern of behavior,
Easy Access

Bigger Phish
Now that phishing scammers are getting better at spelling, it's