Although financial institutions have been developing and implementing Anti-Money Laundering (AML) programs for at least a decade, many still seek to develop more effective practices for identifying and minimizing risk.
The banking sector's groundbreaking efforts to implement controls and compliance in response to laws and regulations such as the Bank Secrecy Act (BSA) and Patriot Act over the last several years has been a great asset to credit unions and to the National Credit Union Administration (NCUA) for responding to financial crime threats.
However, following the recent financial crisis, credit unions and the NCUA must also increase their efforts to develop customer identification programs (CIP) and, as stated by the Bank Secrecy Act (BSA), employ a "risk-based assessment of customer risk." This is not only due to increased regulatory scrutiny, but also to a realization that credit unions have unique characteristics and members, thus requiring strategies specific to their business sector.
In response to this scrutiny, CUs' BSA/AML compliance and identity-theft prevention programs, member screening and risk scoring can help them guard against operational and compliance risks, protect them from fines associated with noncompliance, and avoid financial and reputational losses tied to financial crime.
In fact, FFIEC examination procedures regarding financial institutions enterprise-wide BSA/AML compliance program are specific in evaluating how well financial institutions assess their own risk. The stated objective in the FFIEC guidance is to: "Assess the BSA/AML risk profile of the bank and evaluate the adequacy of the bank's BSA/AML risk-assessment process." Therefore it is imperative that credit unions develop and improve their assessment techniques.
Carrying out risk analysis will involve the identification of areas that are most vulnerable in an organization, the products that are more likely to be used for carrying out illicit activity and the member segments that require heightened scrutiny.
Gravity's Pull
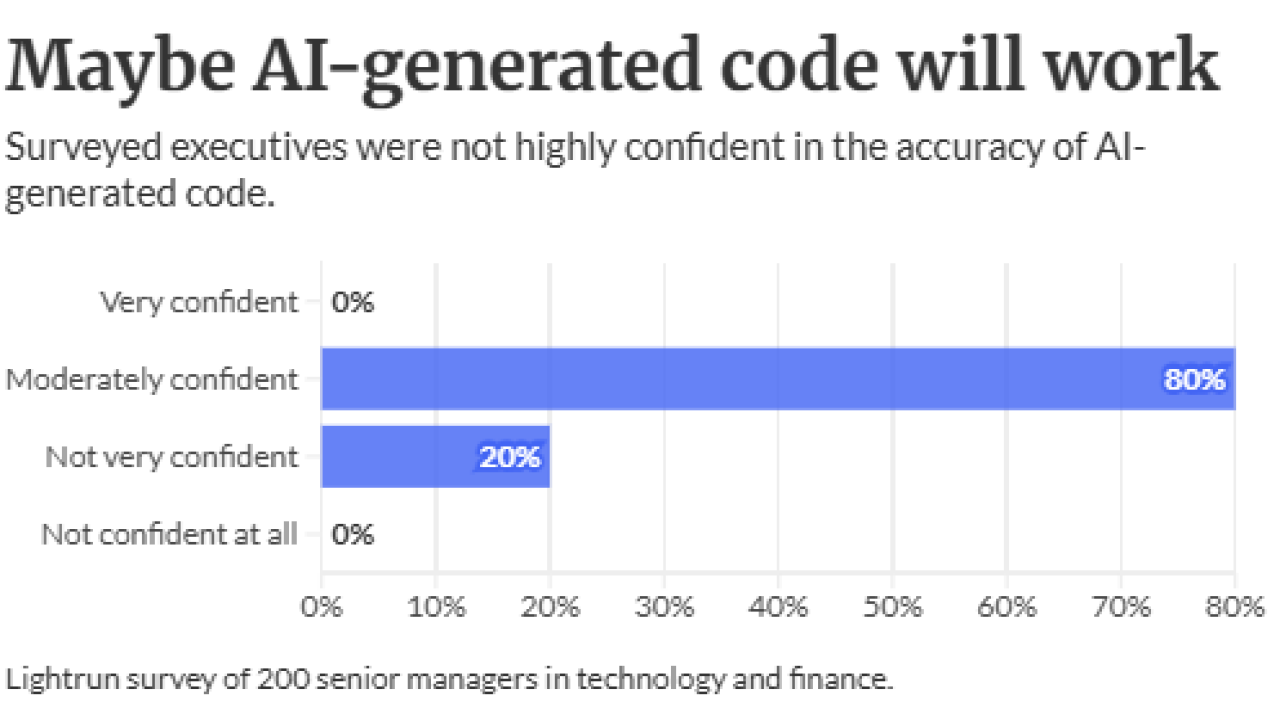
A common strategy for assigning resources and focusing efforts on potential threats is to evaluate the gravity of events that may occur and to respond with an appropriate amount of effort to resolve the event or mitigate the severity of the event's outcome (see chart above).
Potential events or threats can be assigned characteristics. The first being the severity of the occurrence, and the second being the likelihood. Rating events on a scale-or merely assigning levels of low, medium and high-helps to identify the gravest events that, if they were to occur, would represent the greatest impact to an organization. This prioritization will facilitate the decision process around assigning work and formulating more efficient operational activities to quickly disposition these events and take appropriate and rapid action.
This exercise is also a key function for the development of rules-based monitoring of financial activity, high-risk members and accounts, as well as minimizing the time spent addressing any false positive hits. While false positives may be minimized, they are practically unavoidable, because the perpetrators of illicit activity do their best to mimic normal and legitimate financial activity.
Referring back to the FFIEC examination procedures, credit unions can take some pointers from the FFIEC guidance to examiners and use that information to ensure the risk assessment is complete. In reference to "Risk Assessment Link to the BSA/AML Compliance Program," examiners are directed to "...determine whether the bank has adequately identified the risk within its banking operations (products, services, customers, entities, and geographic locations) and incorporated the risk into the BSA/AML compliance program."
The risk analysis should take into account factors such as: as the institution's size and business volume; member profiles; products and business lines; the process of "onboarding" members; and even geographic aspects of member base and business activity.
Also, understanding an examiner's "hot buttons" is an important theme that should run parallel to developing the appropriate controls and procedures based on your risk analysis. The Corporate Examiners Guide (CEG) published by the NCUA will also provide some insights to ensure that your institution is prepared to respond effectively and appropriately during an examination.
Where To Begin
So where should this analysis begin? Let's look at establishing a baseline of areas to be assessed as part of your analysis, then build upon that with some practices to make the resulting risk mitigation and response strategies more robust.
• Perform Risk Analysis: look at a number of aspects that will provide source data and information about your institution, member base, etc., and generate a resulting baseline risk assessment
• Review Results: understand the nature and risk associated with the member base, operational procedures, lines of business, means of interacting with members and, of course, where your institution is most vulnerable and why.
Set Thresholds Based on Results
Keep in mind that:
• Different organizations will have different results.
• Different departments of business lines within an organization may have different results and levels of risk.
• Setting appropriate thresholds allows accounts, transactions, and members to be flagged as high risk for monitoring.
• Understanding where higher risks exist allows for adjusting software tools and processes for greater sensitivity and efficiency (lower ratio of false positives).
Finally, keep in mind that many of the same strategies and efforts to detect unusual financial activity apply to both potential money laundering as well as fraud; and that money laundering often involves compromised individuals who might otherwise not be involved in criminal activity. The Association of Certified Fraud Examiners (ACFE) suggests "there are three elements that enable someone to commit fraud: the motive that drives a person to want to commit the fraud, the opportunity that enables him to commit the fraud and the ability to rationalize the fraudulent behavior."
Where You're Vulnerable
The vulnerability that an organization has to those capable of overcoming all three elements of the fraud triangle is FRAUD RISK. Therefore it is evermore clear why an effective risk analysis, considering multiple factors that are often unique to credit unions versus other financial institutions, is so important.
In next week's installment, we'll discuss leveraging the baseline risk analysis to develop robust risk identification and threat mitigation, while ensuring compliance preparedness as credit unions join their banking brethren on the forefront of financial crime control.
Joseph Bognanno is a financial crimes strategist for Wolters Kluwer Financial Services. He has held positions with the U.S. Treasury, the IMF and other national institutions.