-
Bank executives need to understand these basics of vulnerability and accountability when it comes to the security of electronic networks or they could quickly lose their jobs.
December 2 -
WASHINGTON Federal regulators released a document summarizing their general findings from recent cybersecurity assessments at community-size financial institutions.
November 3 -
New York regulator Benjamin Lawsky may use the cybersecurity rules he's proposed for virtual-currency companies as a model for traditional banks. That would subject the financial institutions his agency supervises to the most stringent data-security rules anywhere.
October 17
New York regulator Benjamin Lawsky has confirmed expectations that his agency's forthcoming cybersecurity examination process for state-chartered banks will be much tougher and more precise than federal regulators' cyber assessments.
One unique requirement: Empire State banks will have to provide the CV and job description of the current chief information security officer or the person filling that role as well as that person's training, experience, reporting lines and an organization chart for the IT and information security functions.
The New York Department of Financial Services will also ask banks to describe how they use multi-factor authentication and how they test new software before putting it into practice, details not normally requested by the federal examiners. And the regulator's
The tougher requirements come as security incidents
"It is our hope that integrating a targeted cyber security assessment directly into our examination process will help encourage a laser-like focus on this issue by both banks and regulators," Lawsky, the department's superintendent, said in a press release. "Cyber hacking is a potentially existential threat to our financial markets and can wreak serious havoc on the financial lives of consumers. It is imperative that we move quickly to work together to shore up our lines of defense against these serious risks."
Lawsky had
Federal regulators have recently begun conducting cybersecurity assessments, but they have adopted a more flexible approach.
The interagency Federal Financial Institutions Examination Council conducted cybersecurity assessments at 500 banks this past summer. These exams focused on network connections, bring-your-own-device policies, threat intelligence and collaboration, cybersecurity controls, dependence on third-party providers and cyber incident management. But they also took into consideration the banks' different sizes, capabilities and exposures.
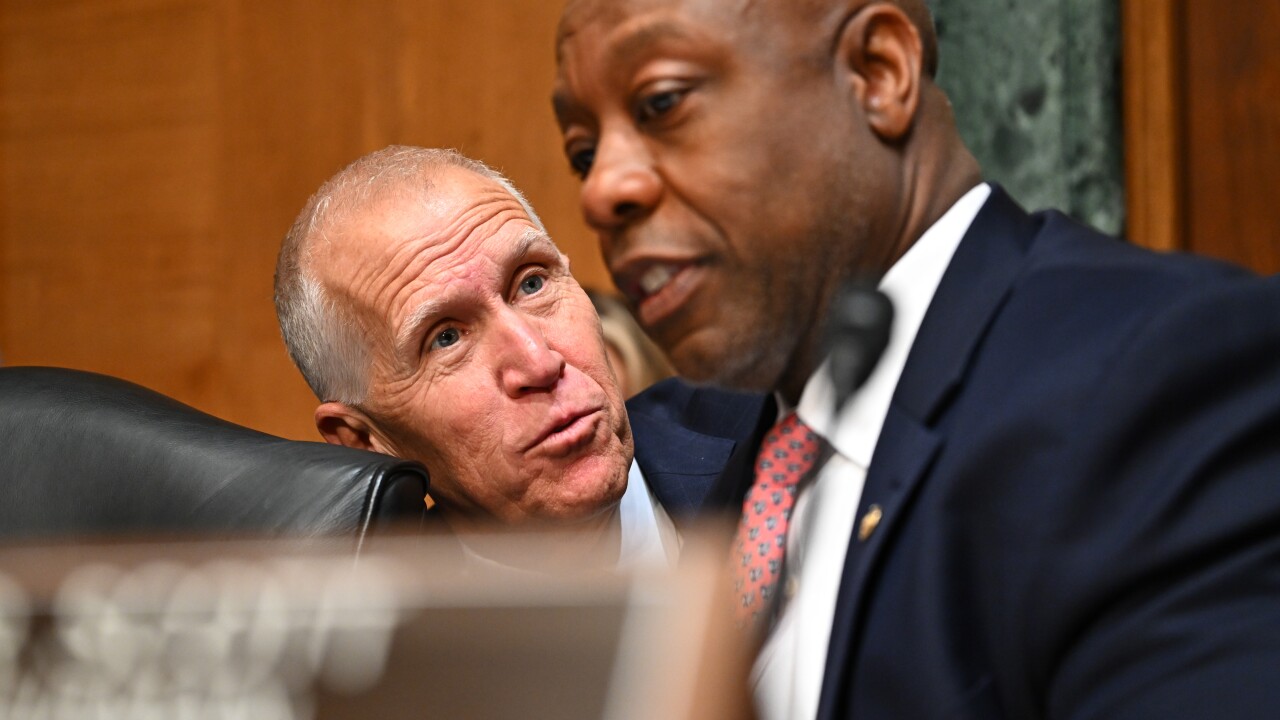
In a Senate hearing Wednesday morning, Valerie Abend, senior critical infrastructure officer at the Office of the Comptroller of the Currency and chair of the FFIEC Cybersecurity and Critical Infrastructure Working Group, said the FFIEC's cybersecurity guidelines "require banks to develop and implement formal information security programs that are tailored to a bank's assessment of the risks it faces, including internal and external threats to customer information and any method used to access, collect, store, use, transmit, protect, or dispose of the information." Large banks that are big targets and serve consumers will be held to a much higher level than financial institutions that are smaller and/or that don't work with consumers.
The New York Bankers Association said Wednesday it was still reviewing the exam process laid out by Lawsky's agency, but complimented him and his staff in a prepared statement.
"The DFS has been at the forefront of the cyber security issue," Michael Smith, the trade group's president and CEO, said. "We will continue to work closely with Superintendent Lawsky on this critical issue, and we look forward to studying the guidelines in depth."
The New York exam will require banks to describe their information security policies and procedures designed to address confidentiality, integrity and availability, and provide copies of the policies. This will force change at many state banks, according to Mercedes Tunstall, partner at Pillsbury Winthrop Shaw Pittman, a law firm based in Washington.
"A lot of financial institutions don't have their policies and procedures addressing these issues, they will generally try to protect data," Tunstall said.
By asking for the CISO's resume and job description, New York regulators are "saying 'this needs to be somebody you take seriously, who has an important role,'" Tunstall said.
The requirement for an org chart is striking, she said, since at many financial institutions, there's often scant cross-reporting and cross-department cooperation.
"In banks, information technology and security may or may not have a relationship to each other," she said. "Something that is clear [from the New York process] is the expectation that they will have relationships with each other, that they won't fight politically internally, that they will have a reporting structure so IT and infosecurity work together."
Another area addressed in New York's exams, multi-factor authentication, "is a very difficult problem to solve," Tunstall noted.
"Even if you use biometrics, that information gets turned into zeros and ones like any other information, and can be hacked anyway. There are some
The requirement that banks describe the application development standards they use "is a fairly strict approach, and it calls for use of a secure software development lifecycle," Tunstall said. Any code that will access sensitive information needs to be developed and tested in a secure environment this is not a common practice in banks today.
"If you don't have that code protected, someone could hack in, see how you're using it and build software code of their own to do the same things," Tunstall said.
New York banks will have to describe a "vulnerability management program" for servers, endpoints, mobile devices, network devices, systems and applications.
"Vulnerability management means you've designed your system in such a way that you have firewalls between layers of servers, and mobile devices that can't get past the firewalls," said Tunstall. "It's saying we recognize there are certain types of information and transactions that need to occur within firewalls."
Banks are typically good at mapping out what needs to be protected where for new apps. "What's harder is legacy systems. They may or may not trace how the app works within the system," Tunstall said.
Some of the components of the New York exam mirror the federal regulators' assessments, however.
For instance, New York banks are being asked to describe how data classification is integrated into information risk management policies and procedures also a requirement of the FFIEC.
"What it comes down to is, most banks have variations in master services agreements with vendors," Tunstall said. For instance, a provider of paper towels will have no access to customer information; a core systems provider will have a lot of access to customer data.
"The challenge is that often the IT folks are the ones that are setting up servers and deciding this information should be on this server or that cloud," and therefore, doing the nuts and bolts of classification, Tunstall said. "Whereas information security people are saying, 'we need to give you the direction. You shouldn't have this information on the same server as that.'" Battles between IT and information security occur regularly over such issues, Tunstall said.
Another New York requirement, that banks explain how they handle patch management and identity and access management systems, involves basic best practices most banks already follow.
The New York exams will scrutinize banks' due diligence around third-party service providers, something the FFIEC also does.
New York banks will have to provide an incident response program, including how incidents are reported, escalated and remediated.
"Most banks have this, and they'd better," Tunstall said. Remediation is a weak spot for some banks, she said. "Sometimes they'll say, 'this seemed like it was a threat but then it wasn't, so we moved on.'"