Be honest. The Bruce Livesays of the world were right.
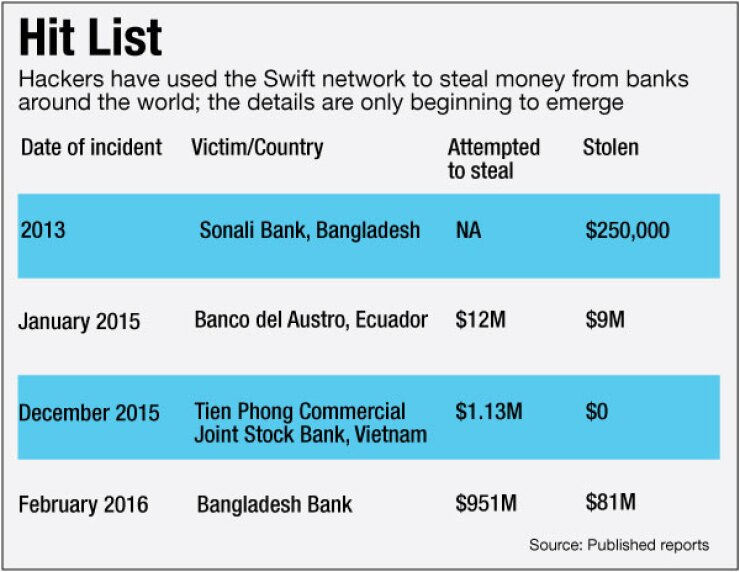
When the chief information officer of First Horizon National in Memphis, Tenn., read about a cybertheft of $81 million from the Bangladesh Bank's account at the Federal Reserve Bank of New York in February, and that the hackers may have gained access to the payments-related messaging system Swift, he swung into action.
Livesay began a review of First Horizon's own Swift environment, paying particular attention to potential vulnerabilities tied to usernames and passwords. Yet he has sensed his banking peers have been slow to react, even as reports of Swift-related incidents have multiplied.
-
A recent spate of breaches on Asian banks that allowed hackers access to the Swift network have resulted in finger pointing, and some calls for creating a new, more secure network. But the issues faced by Swift would likely be the same with any replacement network.
May 29 -
The rub is that the global messaging system's security is only as strong as the weakest link.
May 13 -
Ramamurthi has transformed a 123-year-old institution with one branch serving a dusty Kansas town into a seedbed for disruptive financial technology not to mention a wildly profitable generator of fee income.
December 17
"Initially a lot of people wanted to say it was an isolated incident," he said. "Some people might be lulled into overconfidence that these things are not occurring in the U.S., they're occurring in Asia and the Philippines, where banks in some cases might be less secure than we think we are in the U.S."
If true, it appears the complacent ones made a bad call, especially after word last week that the hostile North Korean government might have been involved in some of the breaches.
Normally in a crisis banks are quick to say they are on top of it, but officials at many banks contacted for this story — with a few notable exceptions — were reluctant to discuss the breaches that allowed access to the Swift network, their reactions to it, or what questions they might be getting from regulators. Perhaps the silence means they are still getting their arms around the problem.
One would think, after the legal, PR and other costs associated with payments-related breaches in recent years at U.S. retailers, banks would be ready for this sort of thing — or at least have well-scripted assurances.
Many of them nod to third-party risk as part of the "risk factors" section in their annual reports each year. They say essentially the same thing — despite their own commitment to securing themselves, the interconnectivity of the financial system poses risks.
For instance, Citigroup said in its annual filing in February that "because financial institutions are becoming increasingly interconnected with central agents, exchanges and clearing houses, including as a result of the derivatives reforms over the last few years, Citi has increased exposure to operational failure or cyberattacks through third parties."
The scariest part is the realization that there are no simple precautions or easy fixes.
"People don't understand the magnitude of Swift," said Suresh Ramamurthi, chief technology officer of CBW Bank in Weir, Kan., which is a member of the network. "Outside of the U.S., every bank has a Swift ID. There's no alternative way to get every bank in the world. … How are you going to get all of them to buy into something new?"
Yet at least a few are taking a shot at strengthening their shields in the short run while pondering longer-term options.
What Big Banks Are Doing
Over the past few weeks, JPMorgan Chase has taken steps to limit employee access to the Swift payments system, according to a person familiar with the matter.
JPMorgan grants different levels of security access to the Swift system. While some employees have permission to only view activity on the system, others can work in it directly.
Following the cyberattacks, the company reviewed the security rights that each employee has to the Swift system, and scaled back the number of employees who have direct access.
The review was not directly tied to a specific concern about JPMorgan's vulnerability to an attack, the person said.
News of the internal review was first reported by the
Regional banks that use the Swift system say they are on the case, too, but offered few details.
"BB&T is vigilant about monitoring for external cyberthreats and we have multiple layers of security safeguards and dedicated teams in place to protect our clients' accounts and financial assets," a BB&T spokesman said.
But Livesay at First Horizon provided a glimpse into his response.
"We looked at how do we have this configured," said Livesay, whose $26.9 billion-asset bank has an international division. "Do we have it on a separate network, what software are we using, how do we manage user IDs and passwords and make sure we do authentication correctly. Things like that." User-access controls, especially administrative rights, called for special attention so that anyone with a random user ID and passcode cannot get in, he said.
In its Swift environment, First Horizon uses a tool called CyberArk that allows a separation between the user ID and password. "The tool prevents people from knowing what their own password is," he said. "They couldn't even give up their password inadvertently because they don't know it."
The software also records every action the user takes. Computers running Swift software are blocked from networks other than Swift's.
At the end of the review, Livesay felt the bank did not need to make changes.
"It does increase our awareness of the risk of this and we're looking at other ways to make sure it's locked down tight," he said.
Why Small Banks Care, Too
A handful of community bankers say they are monitoring the issue, also, either because they are in niche businesses that use Swift or because they fear spillover regulatory risk.
The $2.4 billion-asset Stonegate Bank in Pompano Beach, Fla., uses Swift because of its business with Cuba. Stonegate in May 2015 received approval from the U.S. State Department to open a banking account from the Cuban government.
Stonegate has had no issues with Swift, Chief Executive Dave Seleski said.
"Our volume is very low with Cuba, so it easy to monitor at our end," he said. "Since it is Cuba, it is highly monitored by the regulators. [I am] not sure if it would be feasible to do more than we already are doing" and thus Seleski is not contemplating any changes.
Rusty Cloutier, the president and CEO of MidSouth Bancorp, said that being the head of a community bank means thinking about cyberthreats in much the same way one thinks about weather hazards — as nigh-unstoppable disasters for which a recovery plan is essential.
"I don't know that there's a whole lot that we can do about it except continue to monitor our security very, very tightly," Cloutier said. "I can't control tornadoes, the rain, hurricanes — and I can't control cyberattacks."
He is far from complacent, however. In the past few years he has added two full-time employees to his security staff who spend all day watching the bank's network, looking for holes. He makes sure that they attend industry conferences and read government briefings to learn about the latest threats. And he meets once a month with the team to discuss how to keep the institution running in case of disaster.
The problem, Cloutier said, is that security vulnerabilities often are not identified until after they have been exploited — if not at MidSouth then at some other bank.
The $1.9-billion MidSouth is not large enough to use Swift. But the recent security breaches and resulting thefts are nevertheless worrying for Cloutier. Besides making plain the persistence and ingenuity of cybercriminals, such breaches tend to inspire new laws and regulations, the brunt of which, he fears, could fall on community banks like his own.
"My worry is always — when I hear of a problem at a larger bank — is how much pain am I going to have to take for what they didn't do," Cloutier said.
Braced for Regulators to Weigh In
Any new action from regulators will probably focus on procedures and processes related to those aspects of bank operations that face the international payments system, since that has been the source of the recent hacks and is the venue that can cause the most damage from a systemic perspective, said Heath Tarbert, a former Treasury official who is now a partner with Allen & Overy.
"The interface between the bank and the payment system is one of those areas where, if hackers use it in the right way, they can make a fortune, they can destabilize the bank, all sorts of things can occur," Tarbert said. "I think you're going to see far more scrutiny on the protection and procedures … ensure that those aspects of the IT system are protected and from a personnel standpoint."
But Doug Johnson, who oversees risk management policy at the American Bankers Association, said that he expects regulators to take a "wait-and-see" approach, at least for now, to see what actions the banks take themselves and whether they are appropriate.
Hackers have been using various methods to make unauthorized wire and Automated Clearing House transfers from bank customer accounts for years. The likely next step is for banks and regulators to apply the same lessons from those attacks to the interbank transfer system, he said.
"I think the agencies have been closely watching," Johnson said. "One of the things they recognize … is this type of attack is very similar to what we've seen for years [against bank customers]. The new wrinkle is the banks are the customers."
Kevin Petrasic, a former official with the Treasury and Office of Thrift Supervision who is now a partner at White & Case, said that these issues will likely play out as part of the regular supervisory process. Regulators may not develop a specific rule or guidance related to the Swift system, but whatever industry-identified fixes may emerge could be subject to supervisory scrutiny, with an added emphasis on large or systemically risky banks.
"If you're being told there's a vulnerability, this is how you fix it, and you put off for three or four days something you should have done immediately, that will not be viewed favorably by the regulators," Petrasic said.
Tarbert said that banks would be well advised to take any fixes that are identified through the Swift hacks seriously, because it demonstrates a serious weakness in the payments system — one that could be fatal if either the bank that was targeted were smaller or the amount that is stolen is larger.
"It's a big wake-up call," Tarbert said. "This is a bank robbery — a cyber bank robbery. I think in that respect it represents something new, and in this particular case it's a cyber bank robbery of a central bank. If a community bank lost $80 million that would be catastrophic."
Bank-End Vulnerabilities
Despite the attention on Swift itself, the ball seems to be in banks' court.
The hackers have broken into banks' internal systems, not the Swift network itself, Livesay noted.
Ramamurthi is among those who offer a strong defense of Swift.
"The issue with Swift is no different from the issues with security in using any third-party system for messaging relating to fund transfers," he said. "Once messages are on a multihop system such as Swift, which uses hardware security modules for encryption, they are quite secure. They are vulnerable before they get on to the system and after they get off the system."
There is no secondary verification or confirmation once the message is on the network. If the message is compromised at the sending institution, it will be transmitted on the network — there is no way to know the "hops" it takes along the network and track it down for verification, he explained.
What happened in Bangladesh was an internal hack, Ramamurthi said. The message was compromised before it got to Swift. "Swift is going to say hey, it's not my fault. It's on your side, you're supposed to keep an eye on this," Ramamurthi said.
For its part, Swift says it is being transparent with its users about what has happened and what steps banks should be taking to protect themselves.
"We are sharing information on fraudulent payment cases known to us, notifying our community of any related malware used in customers' local environments and providing indicators of compromise and relevant updates so that customers can better target preventive and detective efforts," a spokeswoman said in an email.
She said the majority of banks' questions are technical or operational, as they try to ensure they have the most up-to-date measures in place.
She added that Swift's guidance is a "baseline" and that "given the sophistication and likelihood of ongoing threats, institutions should take all cyber prevention measures they deem necessary as a matter of urgency."
The organization is also trying to foster collaboration to help it solve issues as they arise and identify patterns.
"Information sharing is key, which is why we are urging customers to share critical security information related to Swift with us," the spokeswoman said.
What Else to Do?
The receiving bank could potentially do extra authentication. The $22.7 million-asset CBW requires two-factor authentication for Swift transfers; Ramamurthi did not want to get specific about what kind. And if a client is trying to send money to an entity that's not a preapproved beneficiary, the bank will stop the transaction and take a second look. The bank also uses statistical modeling to try to find red flags on transactions.
However, Ramamurthi doesn't blame the New York Fed for not requiring two-factor authentication on the Bangladesh Bank wire transfers, or for failing to catch the fraud quickly through fraud analytics. "The Fed can't do it because the Fed is doing hundreds of millions of transactions," he said. "It's not their job to police every central bank."
CBW Bank keeps the server it uses for Swift wire transfers in a separate room protected with an access control system that requires facial recognition to enter. Inside, the server can access only the Swift network, not the Internet at large. All Swift data is encrypted.
All of this was done "a while ago because we wanted to have a complete lockdown," Ramamurthi said.
Although some fintech companies claim to offer an alternative to Swift, Ramamurthi does not see anyone providing a real alternative anytime soon.
Livesay also sees few other choices. "There aren't many alternatives out there today that have these industrial strength, ready-for-mass-use networks like this," he said.
In the end, banks that use Swift or belong to other networks that are only as strong as their weakest links will have to take precautions and perhaps be ready to act faster next time when the new threats emerge. And even then, there are no guarantees.
The attacks that came to light in the past few weeks "probably got everybody thinking this is an area of vulnerability that people need to pay a lot of attention to," Livesay said. "You have to wonder: Can you build something so sophisticated that it can't be fooled? The bad guys are always upping the game, so it's a game of leapfrog."
Brian Patrick Eha, Andy Peters, Robert Barba and Paul Davis contributed to this article.













