Skimming crimes — and their costs — are rising.
Banks are taking notice, teaching customers and employees ways they can thwart devices that tamper with payments hardware to steal data from cards during swiping. Vendors, for their part, are incorporating anti-skimming technology into new automated teller machines and point of sale terminals.
But the problem is not likely to go away soon. "Skimming is a growing issue affecting all of the financial services industry," said Alicia Moore, a senior vice president in charge of ATM banking at Wells Fargo & Co. "It will continue to grow, and we need to proactively stay ahead of the activity as best we can."
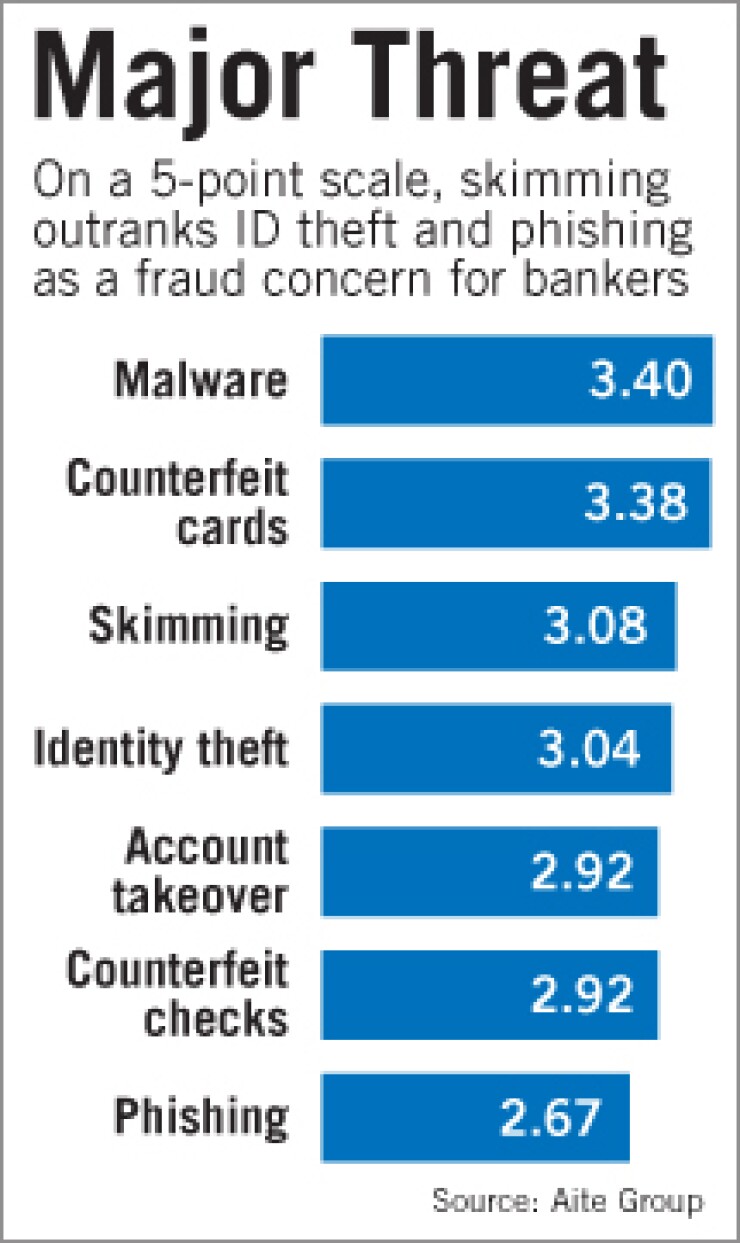
According to Aite Group's report "Enterprise Fraud Management: Investments in Integration," released Wednesday, card skimming was banks' No. 3 concern by severity of losses. The top concern was malware, followed by counterfeit credit and debit cards.
"Skimming is increasing in severity as organized crime sees there is low-hanging fruit" with unprotected magnetic stripe cards in the U.S. market, said Julie Conroy McNelley, senior risk and fraud analyst for Aite and one of the report's authors. McNelley said the average cost to banks of a single compromised ATM is $50,000.
Gartner Inc. reported that at mid-2010 fraud from counterfeit debit cards was up 100% from a year earlier, to 4 basis points, as a proportion of total sales. Skimming is behind the majority of costs from counterfeit debit cards, said Avivah Litan, a vice president and distinguished analyst at the Stamford, Conn., research firm.
The problem is not necessarily whether banks are properly securing their ATM networks, but where their cards are being used, Litan said. "Skimming can happen anywhere," she said. "If you have a huge ATM network, and if you upgrade yours, your cards can still be skimmed at someone else's."
Litan said skimming is so pervasive that banks have been reluctant to make costly ATM upgrades.
First State Bank in Barboursville, W.Va., has just six ATMs. The bigger problem for First State was customer use of debit and credit cards outside its own network, said Sam Vallandingham, the bank's vice president and chief information officer. Over the past two years, nearly 40 bank customers were victimized in a skimming scam when they used their cards to buy meals at a local restaurant.
"The restaurant was fined by Visa because the entire staff was skimming," Vallandingham said. In the past year, incidents of fraud at the $250 million-asset bank, including skimming, rose about 30%, versus a 10% increase in 2009, he said.
"Small banks can't always look at the macro level at all their customers," said Cary Whaley, vice president in charge of payments and technology policy for Independent Community Bankers of America.
Whaley said that in addition to the continuous monitoring of customer data to fight fraud, hardware upgrades are expensive for smaller banks.
Even Wells Fargo, with more than 12,000 ATMs covering most of the country, said it is not ready to commit to using some of the newer anti-skimming technology it is evaluating.
"We continuously update our hardware on a regular cycle," Moore said. But "we have a long road to pilot and test those things out, because we want to be very sure we [use] something that works."
To protect its ATMs from skimmers, Wells Fargo relies on a set of best practices, Moore said. For example, in areas the bank has identified as potentially high-risk — usually a combination of high customer traffic or remoteness of the machines — the bank displays an image on the screens of its ATMs to show consumers what a proper ATM card reader should look like, so they can identify if theirs has been interfered with. "We are targeted in sending those messages," Moore said. "We balance between consumer education and prevention."
Wells also instructs its branch workers to inspect ATMs daily for signs of tampering.
The issues are different for community banks, which typically have smaller ATM networks and fewer resources.
Experts say shifting from magnetic stripe to the EMV Integrated Circuit Card Specifications, commonly called chip-and-PIN, would defeat much of the current card skimming for point of sale transactions.
They point to improvements in fighting skimming in the U.K., where fraud losses on cards fell 28% in 2009 after the introduction of chip-and-PIN technology, according to data from the U.K. Cards Association.
"Criminals have migrated to where it is easiest to commit fraud," said Steve Brunswick, transaction strategy manager for Thales e-Security Inc., a company that helps top banks secure and encrypt ATM transactions. Brunswick said it has become harder to commit skimming fraud in countries where chip-and-PIN technology has been introduced, but "the U.S. remains a softer target."
ATM vendors and security companies are pushing various offerings to make machines more secure. ADT Security Services Inc. in Boca Raton, Fla., offers a box that interrupts the signals a skimmer depends on to read magnetic stripe data, and it also acts as a burglar alarm. The box is based on technology from TMD Security Group Inc. of Scarsdale, N.Y., and can be installed at any ATM.
But retrofitting ATMs costs $2,000 to $2,500 per machine for the TMD technology alone, according to ADT.
Diebold Inc. of North Canton, Ohio, has a number of anti-skimming products and services. As a short-term fix on its new machines, it has changed the shape of the card slot bevel, making it more difficult for criminals to attach a reader. It also uses the TMD sensing technology that ADT uses.
Diebold said the TMD product has been standard on all its newer "motorized" ATMs for the past 18 months and optional for its dip-card machines. "There is no one solution" to skimming, "and we believe in layered security," said Chuck Sommers, vice president of ATM security and systems for Diebold.











